Google rushed out a Chrome update in February 2026 after attackers actively exploited CVE-2026-2441 in the wild. The flaw could let attackers execute code through malicious web content, so a normal webpage visit could start a compromise. For businesses, that means browsers remain one of the easiest entry points for attackers. That is exactly why strong Web Protection matters.
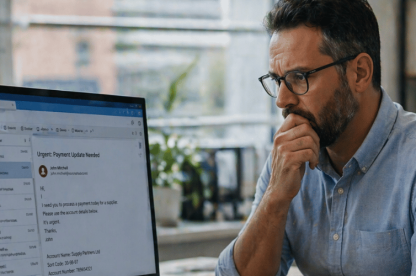
Staff use browsers to sign into SaaS platforms, open email links, access portals, download files, and move between cloud tools all day. For SMEs, that turns the browser into a routine point of exposure.
TrustLayer Browse fits here because stronger Web Protection helps businesses cut exposure before a malicious page turns into a wider incident. For most businesses, patching alone won’t close the whole gap. Some devices stay exposed for a time, which is why businesses need another control before users reach risky content.
What happened in the Chrome zero-day, in simple terms?
CVE-2026-2441 was a Chrome zero-day that attackers were already exploiting before Google released a patch. For businesses looking for a plain-English explanation of the Chrome zero day vulnerability, the key point is simple: attackers were already using it before the fix was widely in place. Security reporting said the flaw could let attackers execute code through crafted web content, so a malicious webpage could trigger dangerous behaviour inside the browser.
Security teams may need the technical detail. Most businesses need the practical takeaway. Attackers turned web content itself into the attack path. That is why businesses need to push urgent browser updates quickly.
Why should businesses care about a Chrome zero-day?
The browser is part of normal business work
Most SMEs rely on browsers for far more than casual web use. Staff open cloud platforms, accounting tools, CRMs, shared files, admin portals, and collaboration apps through the browser all day. That puts the browser between the user and the systems the business relies on most.
When attackers actively exploit a browser flaw, everyday browsing becomes a real business risk. A malicious webpage is not a niche technical problem. An employee could reach it while doing ordinary work.
Small teams do not always patch every device immediately
Patching is essential, but many smaller businesses do not update every machine at once. One IT lead or a small internal team may still be checking laptops, shared devices, and remote machines after Google releases the fix.
That leaves a gap between Google releasing the fix and the business actually closing the exposure.
One malicious webpage can still lead to a wider problem
A browser exploit does not stop at the page itself. Once a malicious site triggers code execution or unsafe browser behaviour, the attacker can move from the page to the device or into the user’s session.
That is why browser vulnerabilities matter to businesses of every size. The page only opens the door. The attacker still needs a route forward, and the browser can provide it.
How do zero-day browser exploits work?
In simple terms, a user visits or gets redirected to a malicious webpage. The browser processes crafted content. The flaw lets the attacker trigger code execution or unsafe behaviour inside the browser.
That gives the attacker an opening. What happens next depends on the exploit chain. One page view can still become a wider security problem when the browser is vulnerable.
Is patching enough to protect your business from a Chrome zero-day?
Patching is essential. When Google releases an urgent update for an actively exploited flaw, businesses need to move quickly.
Why urgent patching still matters
An unpatched browser leaves known exposure in place. If attackers are already exploiting a vulnerability in the wild, every delayed update keeps the business open to that risk for longer.
That is why businesses should apply Chrome updates quickly across their devices and verify them, not just assume they landed.
Why patching alone is not enough
Patching still leaves a gap. Users continue browsing before every device is updated. Some devices update late. Some users keep sessions open. Some machines sit outside normal update cycles.
A browser exploit exposes a broader problem. Businesses cannot rely on perfect patch timing alone. Web Protection will not remove the flaw itself. It can reduce the chance that a user reaches the page or content the attacker needs to trigger the exploit.
Chrome’s follow-up zero-days show this is not a one-off
Google issued another emergency Chrome update in March 2026 for two more zero-days under active exploitation. That matters because browser risk does not stop with one isolated vulnerability. It keeps returning in new forms, and businesses need controls that reduce exposure even while updates catch up.
Could Web Protection stop a Chrome zero-day exploit?
Strong Web Protection reduces the chance that users reach malicious destinations or unsafe content that attackers rely on.
Strong protection can block risky web destinations, filter unsafe content, and apply browser-use policies before a page starts a wider incident. For SMEs, that means less dependence on perfect patch speed and less time spent chasing exposure after it has already started.
This is where TrustLayer Browse helps. It gives businesses stronger control over risky web activity and unsafe destinations before the issue spreads further.
What should SMEs do after a browser zero-day is disclosed?
After a browser zero-day is disclosed, SMEs need to move quickly. Patch first. Then reduce exposure and give users simple guidance. If you are looking for practical CVE-2026-2441 mitigation steps, that is the right order to follow.
Update Chrome quickly across the business
Apply the patch as soon as possible. Confirm that business devices actually updated. Do not assume every browser updated itself properly.
Reduce browser exposure while patching catches up
Use stronger Web Protection to limit access to risky destinations and unsafe content while updates roll out. That reduces the chance that one delayed patch becomes a wider problem and helps with preventing malware from Chrome zero-day exploits before users reach the page that starts the chain.
Give users simple, useful guidance
Keep user guidance practical. Treat suspicious links carefully and report unusual browser behaviour. Do not overload staff with technical detail they cannot use.
Make browser risk part of layered defence
Put the browser inside a wider security model. Web protection and endpoint controls reduce browser-based risk at different points. User awareness and broader visibility still matter.
Why does Web Protection matter against browser-based attacks?
Browsers remain one of the most exposed parts of daily business activity. Attackers still use malicious webpages, redirects, compromised sites, and unsafe downloads to reach users.
That is why Web Protection matters now. It gives the business another control point before a page turns into a compromise.
SMEs cannot rely on perfect patch timing alone. They need practical web protection that reduces risk while staff continue doing normal work.
How does TrustLayer fit into this?
TrustLayer Browse helps businesses tighten Web Protection by controlling access to risky web content and unsafe destinations earlier. That is the gap many smaller businesses struggle to close when attackers exploit browser vulnerabilities in the wild.
That helps the business cut exposure before a malicious page turns into a wider incident. If the business needs broader layered coverage across web, email, users, and cloud, TrustLayer One gives that wider platform view.
See where your browser exposure starts
If browser risk is the immediate gap, start with TrustLayer Browse. That gives the business a practical way to cut exposure before users reach unsafe pages or risky destinations.
The real lesson is not just to patch faster. It is to reduce browser exposure earlier
The Chrome zero-day is a reminder that the browser remains a live attack surface. Patching is essential, but it is not enough on its own.
Businesses still need Web Protection that reduces exposure before malicious web content leads to a wider compromise. Cut the chance that users reach risky content while updates catch up. That gives the business more control while patching still catches up. Then fold web risk into the broader security model.
If browser exposure is the immediate concern, start with TrustLayer Browse. If the challenge is broader and touches web, email, users, and cloud at the same time, move up to TrustLayer One.