A recent AI-assisted cyber attack campaign in the UAE showed how quickly attackers can coordinate phishing, infiltration attempts and ransomware-style activity at scale. UK SMEs should pay attention because AI lets attackers move faster and produce more convincing lures. That is exactly why Web Security matters to UK businesses with lean internal security resource. The risk rises once a user reaches a fake login page or downloads unsafe content.
Many UK SMEs will see a story like that and assume it sits outside their risk profile. Large-scale incidents targeting government systems do not always look relevant to a small or mid-sized business. But the lesson is simpler, and it applies directly to cyber attack preparedness for SMEs. AI helps attackers move faster and produce more convincing campaigns with less effort.
Many smaller businesses do not have a dedicated security team, a round-the-clock monitoring function, or the time to manage a long list of separate tools properly. One IT lead or a small team often must cover support, access issues, and security at the same time. That makes earlier control and earlier visibility more important.
How is AI changing cyber threats for small businesses?
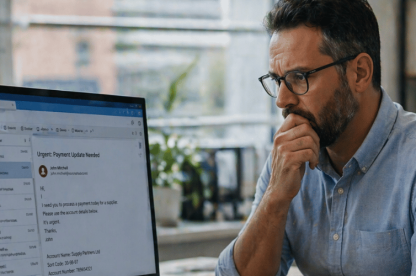
This is the part many small teams need to understand first. How AI changes cyber threats for small business is not an abstract issue. It affects how quickly attackers can build lures, how convincingly they can imitate normal business communication, and how fast a suspicious event can turn into a real incident.
Why is phishing getting harder for staff to spot?
Phishing used to be easier to dismiss when messages were badly written or obviously suspicious. AI has changed that. Attackers can now generate emails and fake login prompts that sound more natural, contain fewer obvious errors, and feel more relevant to the recipient.
Not every phishing email will suddenly look perfect. The bigger issue is that the average standard improves. Businesses that still rely on users spotting warning signs on their own will miss more of them.
How does AI help cyber attacks move faster?
AI also helps attackers build and test campaigns faster. That shortens the time between the first message and the point at which IT needs to respond.
For SMEs, that timing matters. A small team may not review suspicious activity continuously, and by the time someone investigates, the issue may already stretch beyond the original email or website visit. A user may have entered credentials, triggered a malicious download, or left an attacker with an active session. That is often the point where a suspicious event turns into an active incident.
Why can one click lead to a wider incident more quickly?
The first phishing email or suspicious website is rarely the whole problem. The more serious issue is what happens after that first interaction. Once a user reaches a fake login page or enters credentials, the incident can escalate quickly. Attackers may reuse those credentials, introduce malware, or trigger internal disruption.
Web security for SMEs needs to act before the user reaches risky content. Once IT starts reviewing the fallout, the response is already under pressure.
How can small businesses reduce the risk of AI-powered cyber attacks?
For IT managers, operations leads and small internal teams, these steps are a practical place to start. They also reflect the kind of small business cyber security best practices that still make a measurable difference when attack methods speed up.
Which basic cyber security controls still matter most for SMEs?
AI changes the speed and quality of attacks, but the basics still matter because attackers still exploit easy paths. For SMEs reviewing AI cyber attack prevention strategies in the UK, this is still the starting point. Regular patching and multi-factor authentication reduce avoidable exposure. Clear internal verification processes also matter, and businesses need tighter control over access rights.
These controls need to work together. MFA (Multi Factor Authorisation) does not remove the need to stop users reaching fake login pages in the first place. Patching does not solve poor visibility into risky browsing or unsanctioned cloud use. If a user receives an unexpected login prompt, payment request, or shared file, the business should give them a simple way to verify it before they act. If administrative access is broader than it needs to be, the business should review it before it becomes a more serious issue during an incident. These controls are not new, but they still work.
Why does Web Security matter before a user reaches risky content?
For SMEs, Web Security means controlling access to risky sites, fake login pages, unsafe downloads, and unsanctioned cloud activity before those interactions become incidents. This is one of the few points in the attack chain where prevention is still realistic.
If a user can still reach a phishing page or an unsafe download point, the issue has already moved closer to containment than prevention.
Email security helps stop malicious messages from reaching users. Web Security helps stop users reaching risky destinations when they click links or use cloud services. Each control covers a different part of the problem. For SMEs, TrustLayer Mail and TrustLayer Browse work best when they support the same response model.
Many SMEs still treat web security as basic website blocking. That is too narrow. TrustLayer Browse gives teams earlier control over risky destinations and clearer visibility into what users are actually accessing. That helps businesses reduce exposure to fake login pages, unsafe downloads, and unsanctioned cloud activity before the issue grows.
Why does Web Security matter more when AI-driven attacks move faster?
Web Security is often treated too narrowly. Many businesses still think of it as little more than URL filtering or a way to block obviously inappropriate sites. That is too limited for the current threat landscape.
When attackers use AI to improve phishing and speed up delivery, web security needs to do more than block a shortlist of bad destinations. It needs to cover browser and cloud activity, support remote and office-based users consistently, and show IT teams what has happened when something looks wrong.
For small businesses, that only works if the approach stays practical and manageable. It needs to reduce risk without creating a stack that is difficult to maintain or controls that only work in part of the environment.
TrustLayer Browse fits that need by blocking phishing sites, malware links, and risky domains before users click through. It also improves visibility into cloud app use and shadow IT. For SMEs, that means less manual reconstruction after the event and fewer gaps between the first click and the start of their response. Teams that need broader control across web, email, and user risk can then move up to TrustLayer One.
Why do SMEs need more than one security layer?
Web security is a major part of the answer, but it cannot carry the whole load. Understanding AI-driven phishing and ransomware matters here, because they do not stay neatly in one channel, and that is where smaller teams lose visibility. An email can lead to browser activity or cloud app access before a small team has pieced the sequence together.
Layered defence matters because each control covers a different part of the attack chain. TrustLayer Mail helps reduce the chance that phishing, spoofing, and malicious attachments reach users in the first place. TrustLayer Users helps reduce avoidable mistakes, and user awareness should not be the only line of defence. Joined-up monitoring gives IT teams a clearer view of what is happening and where attention is needed first.
TrustLayer One brings that approach together across Browse, Mail, Posture, and Users. For SMEs with limited internal resource, that joined-up model is easier to manage than stitching together separate tools and hoping nothing important gets missed.
The real lesson for SMEs is speed, not scale
A UAE-style AI cyber attack may sound like a distant headline. But UK SMEs should still take the lesson seriously. The clearest AI cyber threat examples and lessons are often the ones that show how fast a familiar attack chain can become harder to contain. AI is changing how attacks are delivered and how convincing they can appear.
Most businesses will not predict every new technique. They do not need to. They need to close the gaps attackers keep using. Better Web Security and clearer visibility remain two of the most practical ways to do that.
If your current security setup leaves too much to manual review or post-incident response, now is the right time to reassess it. Start with TrustLayer Browse if web risk is the main gap. Move to TrustLayer One if you need joined-up control across web, email, cloud apps and users.