How many cloud apps are your employees using right now? The number is probably higher than you think, and that blind spot is a major security risk. As businesses move to the cloud, the traditional network perimeter has disappeared, leaving a complex security landscape in its wake. This is where a Cloud Access Security Broker, or CASB, comes in. A CASB is a security policy enforcement point placed between cloud service consumers and cloud service providers to combine and interject enterprise security policies as cloud-based resources are accessed. In short, it’s a critical tool for modern cloud application security.
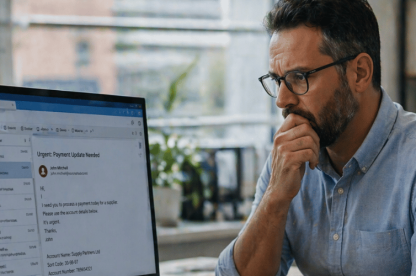
A widely cited Gartner prediction from a few years ago stated that one-third of successful cyberattacks would target data stored in Shadow IT infrastructure. Recent reports have confirmed this has become a reality, with one in three data breaches now involving Shadow IT. This highlights why CISOs, and IT leaders consider human error and unmanaged apps their top security concern.
Ready to find your blind spots and take control of your cloud environment? Book a demo today to see how TrustLayer can help.
What are the main functions of a CASB?
A CASB works by acting as a gatekeeper for your cloud environment, giving your security team a single point of control over a wide range of activities. Its key functions fall into four main pillars:
- Visibility: A CASB’s first and most crucial function is to provide comprehensive visibility. It discovers and logs every cloud application in use across your network, including both sanctioned apps (like Microsoft 365) and unsanctioned “Shadow IT” apps that your team may have adopted without approval. This function is vital for understanding your full cloud footprint. Independent studies show the average company is running close to a thousand SaaS apps outside IT’s visibility. That means when a CASB scan runs, it on average uncovers five to ten times more cloud apps than the IT team thought were in use.
- Data Security: Data Loss Prevention (DLP) is a core component of CASB security. A CASB can inspect data as it travels to and from the cloud, identifying and blocking the transmission of sensitive information, such as credit card numbers or personally identifiable information (PII). This ensures that your company’s most valuable data doesn’t leave your control.
- Threat Protection: A CASB actively protects against malware and other threats that can originate from cloud applications. It can scan files for malicious code as they are uploaded or downloaded, preventing infections from spreading to your network. This is particularly important for an organisation that relies on shared cloud storage or collaboration tools. To see this in action, explore our web protection features.
- Compliance: For businesses in regulated industries like finance or healthcare, maintaining compliance is non-negotiable. A CASB helps enforce policies to meet these requirements by monitoring and controlling access to cloud apps based on user, device, and location, and by generating detailed reports for audits. For example, TrustLayer helped Radius Payment Solutions gain global visibility and control over confidential customer data to meet regulatory requirements.
Why has CASB security evolved beyond traditional tools?
The rise of the cloud has rendered many traditional security tools, such as firewalls and web proxies, insufficient on their own. These tools were designed to protect a well-defined network perimeter, but modern workforces operate far beyond a physical office. Traditional tools simply aren’t enough to provide the robust CASB security needed today.
A modern CASB, on the other hand, is specifically designed for the cloud-first world. It understands the context of an action—not just that a user is accessing a cloud app, but what they are doing, what device they are using, and what kind of data is being moved. This level of granular control is what sets modern CASB security apart and makes it an essential part of a modern security stack.
How does a CASB protect against insider threats and shadow IT?
Shadow IT and insider threats are two of the biggest risks that a CASB is uniquely positioned to address. A recent study found that 55% of companies have experienced a SaaS security incident, and 58% of CISOs estimate their current SaaS security solutions only account for 50% or less of the organisation’s applications. This is why many IT teams feel that enforcing cybersecurity policies is impossible. A CASB can:
- Automatically discover and classify applications. The ability to automatically discover and classify applications is a cornerstone of effective CASB security. This provides your IT team with a complete inventory of every cloud service being used, allowing them to assess the risk of each one and bring them under a managed policy.
- Detect suspicious user behaviour. A CASB can establish a behavioural baseline for each user. If an employee suddenly starts downloading a massive amount of data, attempts to access an application from an unusual location, or shares sensitive information with an unapproved party, the CASB can flag or block the action in real-time. This protects against both malicious insiders and compromised accounts. TrustLayer has helped organisations like a growing UK educational trust gain full visibility into staff behaviour and improve protection for sensitive student data across multiple sites.
TrustLayer helps security leaders turn insight into action. If you’re ready to see how we can bring your Shadow IT into the light and gain full control, why not book a walkthrough with our team?
How does a CASB protect against shadow AI?
Shadow IT isn’t the only blind spot. Increasingly, employees are adopting generative AI and machine learning tools without IT approval. This is being called shadow AI. These services can expose organisations to significant risks, from inadvertent data leaks to compliance violations.
A CASB is uniquely positioned to bring shadow AI into the light by:
- Discovering AI tool usage: CASBs can identify which AI platforms employees are connecting to, even when those tools haven’t been sanctioned.
- Controlling sensitive data uploads: By applying Data Loss Prevention (DLP) policies, a CASB can prevent users from pasting confidential data into AI prompts where it could be stored or reused outside the company’s control.
- Enforcing policies by user or group: IT can allow controlled AI use for certain roles (e.g. R&D) while blocking or restricting others (e.g. HR or finance).
- Providing audit and visibility: CASBs generate detailed logs and reports, giving leaders oversight of AI usage trends and supporting compliance with data protection regulations.
The rise of shadow AI mirrors the early days of shadow IT: adoption is happening fast, but governance is lagging. Without visibility and control, businesses risk sensitive data slipping into systems they don’t own. With CASB security, shadow AI becomes another risk you can manage, instead of a threat waiting to surface.
What are the main benefits of using a CASB?
The functions of a CASB translate directly into significant benefits for your business, simplifying security management while drastically reducing risk.
- It simplifies your security management. Without a CASB, securing cloud usage would require a mix of different tools and a lot of manual oversight. A unified platform is the key to achieving modern CASB security without adding complexity. A CASB unifies these functions into a single platform, giving your lean IT team full control from one console. This centralisation reduces administrative overhead and makes it easier to enforce a consistent security policy across your entire cloud environment. TrustLayer helped St Anne’s Community Services streamline their security by managing CASB, web, and email security from a single platform.
- It dramatically reduces your risk. The discovery of Shadow IT alone is a huge benefit, as these unsanctioned applications are often a major source of security vulnerabilities and compliance gaps. By gaining visibility and control, you can proactively close these gaps before they become a problem. This improved CASB security helps prevent data breaches and unauthorised access.
- It empowers proactive protection. A CASB allows your team to move from a reactive security posture (responding to breaches) to a proactive one (preventing them). By setting granular policies and receiving real-time alerts on suspicious activity, you can stop threats before they cause damage. It’s about empowering users to work productively while ensuring they do so safely.
The result of a well-deployed CASB is a proactive security posture that saves time, reduces admin, and provides tangible peace of mind. To see a full demonstration of these benefits in action, schedule a demo today.
Is a CASB an essential part of my cybersecurity strategy?
If your business uses cloud services, the answer is yes. The proliferation of cloud apps and remote work makes it impossible to secure your network perimeter alone. A CASB provides the visibility and control needed to secure data and users no matter where they are or which application they’re using. If you want to simplify complex cybersecurity challenges for your lean IT team, a modern CASB security solution is your best bet.
With TrustLayer, you can gain this level of control and insight without the complexity. Our platform integrates CASB security with other critical security functions, giving you a unified view of your entire security posture.
Ready to see how we can simplify your cloud security and take the guesswork out of compliance?
Discover how a demo of TrustLayer One can simplify your cybersecurity and protect your business from sophisticated threats.