Shadow IT is everywhere. People bypass IT controls to meet deadlines, share files in unsanctioned ways, or adopt new tools to stay productive. That speed often comes at the cost of visibility and control for security teams. That’s where a Cloud Application Security Broker comes in.
CASB: what is it?
A Cloud Access Security Broker (CASB) monitors and governs cloud activity. It identifies which apps employees use, how they’re used, and what data flows in and out. Known apps like Google Workspace stay managed. Risky or unknown tools trigger alerts or get blocked outright.
For security leaders searching CASB what is it, this blog brings practical answers from real-world implementation.
When does a business need a CASB?
In most organisations, shadow IT starts small until it doesn’t. You might think 40 apps are in play, but a CASB scan often uncovers 200. At that point, you’re no longer in control.
Remote work, personal devices, and strict compliance rules push IT teams to the limit. If your team can’t see where data’s going, you can’t secure it.
The right question isn’t just what is CASB, but when do I get it? The answer: before a cloud blind spot becomes a breach.
Why Is Shadow IT a Security Risk?
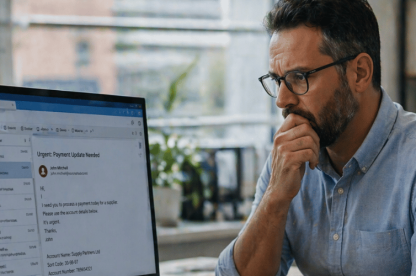
Shadow IT usually stems from good intentions. People solve problems with the tools they know. But those tools may store data offshore, skip multi-factor authentication, or sync sensitive info to personal accounts.
It’s not about blame. It’s about blind spots. A strong CASB shows you what’s happening and where so you can act fast. Think of it as a feedback loop, not a punishment system.
If leadership ever asks, “what is CASB catching that our legacy tools can’t?”, the answer is simple: the human factor.
Key capabilities of a CASB
Good CASBs don’t flood you with alerts. They filter signal from noise and highlight risky patterns like credential reuse, app misuse, or off-policy sharing. Then they let you act. Core capabilities include:
- Discovery of unmanaged apps – automatically identifying sanctioned vs. unsanctioned tools across the business
- Risk scoring and analytics – ranking apps based on usage, configuration, and compliance risk
- Identity-aware controls – tying policies to specific users and devices, not just IP addresses
- Granular enforcement – blocking risky actions (like file sharing outside the organisation) without disabling the whole app.
These capabilities go beyond data loss prevention. They give IT leaders real-time intelligence that scales with how people use cloud tools.
What are the most common CASB use cases?
We’ve worked with teams who discovered accounting staff using five file-sharing apps across two continents. Not one was approved. Sensitive data was at risk. No one realised until a CASB audit flagged it.
Other examples include redacting financials uploaded to public drives, blocking logins from suspicious geos, and enforcing stricter controls during mergers. CASB gives you the tools to act, not just observe.
They’re vital during breach investigations. When an incident occurs, you need to trace actions fast: who, what, when, and where. CASB provides that forensic clarity.
If you’re still asking “CASB, what is it, what do I need it for”, begin by looking at the areas of cloud activity you can’t currently account for or explain.
TrustLayer’s CASB in Context
TrustLayer’s CASB is a core part of TL Browse but also works alongside TL Posture and TL Users giving teams a layered, real-time view.
As part of TL Browse, CASB:
- Detects shadow IT automatically
- Scores both app-level risk and in-app actions, powered by a catalogue of thousands of pre-classified applications
- Expose risky apps and behaviours as they happen
Built to run fast and adapt without slowing users down, TrustLayer fits into how teams already work. If you are still wondering “CASB what is it doing in our stack” or “what is our CASB actually doing” you should be worried. It should be catching shadow IT, scoring app risk, and tying identity to access. If it’s not, you’re flying blind.
CASB as part of TL Browse, and alongside TL Users and TL Posture give teams a real-time picture of cloud, user and app activity, turning blind spots into controllable risks.
How TrustLayer delivers
TrustLayer’s CASB can be deployed both inline (with via an agent or gateway) or via API connectors. Our DirectProtect Browse architecture uses a proxy-less approach, connecting directly to cloud traffic without rerouting, decrypts when configured, and monitors for high-risk signals including:
- Unmanaged app logins
- Risky OAuth connections
- Data exfiltration attempts
This proxy-less approach means you can enforce controls without introducing friction for users. IT can block risky apps and actions within them, adjust controls as behaviour changes, and stay ahead of emerging threats.
Real results with TrustLayer
Case Study: St Anne’s Community Services
1,200 staff. 150 sites. A lean IT team. They needed better visibility across cloud, email, and endpoints.
With TrustLayer, they:
- Detected unmanaged apps fast
- Centralised incident response
- Closed policy gaps across teams
The result? A 43% drop in unsanctioned tool use in just two months. No disruption. No extra workload. See full story.
Looking to do the same? Let’s talk.
What happens without a CASB?
Without a CASB, your security is half blind. Apps get used. Risky actions taken. Data gets shared. Logs go missing.
Most teams don’t realise what they’ve missed until a breach or failed audit forces them to find out. That’s why visibility matters.
How does a CASB compare to traditional security?
Firewalls protect your network. VPNs secure remote connections. Legacy tools handle endpoints and email. But none of them see what happens inside cloud apps.
That’s where CASB comes in. It monitors SaaS and cloud activity, sets rules tied to identity and behaviour, and enforces them in real time. The result: you control cloud risk without piling on complexity.
CASB what is it doing that your legacy stack can’t?
Is a CASB optional?
No.
If your business uses cloud services, you need visibility. You need control. You need evidence that your policies work. A CASB is no longer a nice-to-have, it’s the backbone of a cloud security posture that can scale.
What is CASB helping you prevent?
Think compliance failures, insider mistakes, and public leaks. But also think reputation damage, lost trust, and operational chaos that can follow a preventable breach.
With TrustLayer, you:
- Expose Shadow IT and know the apps being used on your network
- Block the app itself, or high-risk specific actions within the app
- Prove you’re in control with easy, fast reporting
Seamlessly integrated within TrustLayer One, you also gain the confidence to pass audits faster, onboard new SaaS tools securely, and say yes to business innovation without worrying about data sprawl.
Book a demo and see it in action.