From 31 March 2026, organisations will no longer receive findings from the NCSC’s Mail Check and Web Check services since the NCSC (National Cyber Security Centre) is retiring both services. The NCSC strongly recommends organisations implement a commercial External Attack Surface Management product before the retirement date, so they do not lose visibility into internet-facing exposures and misconfigurations.
Web security solutions feel too reactive when they alert after the browser session has already happened. IT departments then reset credentials, check endpoints, and manage exceptions while the business asks why controls changed after the incident.
Businesses need web security solutions that reduce exposure at the point of access and keep enforcement consistent on off-network devices. TrustLayer Browse supports this model by applying endpoint enforcement and keeping reporting usable, which helps IT departments tighten policy without creating a flood of noise.
What does “reactive” web security look like in real environments?
Reactive web security responds after a trigger. That trigger might be a malware signature, a reputation score that updates too late, or a policy that only applies on-network.
Common reactive failure modes include:
- Blocking a domain after users already visited it
- Detecting a download after it reached the device
- Alerting on risky browsing behaviour without stopping the session
- Enforcing policies on office networks but losing control when users roam
These patterns create a familiar workload: triage alerts, reset credentials, check endpoints, then explain to the business why access changed after the incident.
Modern browsing happens everywhere. Staff work from home, use personal hotspots, and access SaaS through browsers that stay signed in for days. Reactive tools treat the web as a series of URLs. Modern risk looks more like sessions, credentials, and the decisions people make inside normal workflows.
Why have web security solutions become too reactive for modern threats?
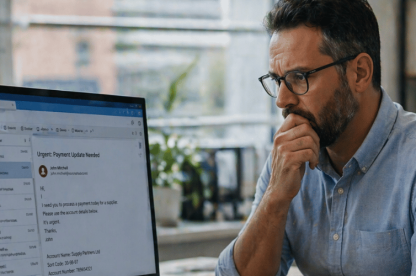
Threat actors change their delivery paths quickly. They register new domains, weaponise compromised sites, and chain redirects to hide the final destination until the last moment. They also design lures that look like routine tasks, such as document sharing, account sign-in prompts, or “view invoice” links.
A reactive control struggles here for one reason: it needs prior knowledge. It waits for a signature, a known bad domain, or a confirmed indicator of compromise. Attackers only need a short window before your controls categorise the destination as risky. Proactive controls block at the point of access, before the session becomes an incident.
The NCSC takes a pragmatic view of browser security. It notes that modern browsers have improved and tend to remain secure in their default state, and it focuses guidance on developing an approach that works for your organisation rather than prescribing per-browser configuration. Organisations need controls that work across users and devices, not alerts that arrive after the fact.
What is the difference between reactive and proactive web security?
Reactive tools show up in tickets and logs after the user already reached the destination. Your IT function then resets credentials and checks endpoints.
Proactive web security solutions change that sequence. They block risky destinations early, keep policy consistent on roaming devices, and reduce how many browser-led events reach investigation.
The test is simple: where does enforcement happen, and when does the tool act?
Reactive controls act after the visit or download, often relying on known bad indicators. Proactive controls act at the point of access and apply policy at the endpoint, so it follows the device.
The Hacker News used this framing to argue for proactive web security over tools that respond after detection. Treat that as industry commentary, then focus on the operational point: the earlier you block the session, the less work follows.
What should you look for in modern web security solutions in the UK?
Most buyers search “web security solutions” when something already feels out of control. That may be a malware incident, users reaching risky content, or limited visibility into what staff access on unmanaged networks.
When you evaluate modern web security solutions in the UK, look for five practical capabilities. Pay close attention to where enforcement happens and how quickly you can push a policy change to every roaming device.
1) Block threats before the click becomes a session
Look for controls that stop phishing pages and malware sites before the user interacts. This is where organisations feel the difference between prevention and response. Blocking late still leaves you with incident reporting and follow-up work.
2) Enforce policy at the endpoint, not only at the network
Your perimeter changes every day. If enforcement only works on office networks, users will bypass it on home Wi-Fi and hotspots, and your reporting will understate risk. A good buyer test is simple: how quickly can you apply a policy change to every device after you see a new browsing risk? Endpoint enforcement helps keep controls consistent across office networks and remote working.
3) Provide usable reporting, not noise
You need reporting that answers operational questions quickly, without forcing your team to stitch together logs across tools. If a report does not help you decide what to block, what to allow, and who needs follow-up, it creates noise.
- Which categories and destinations drive risk?
- Which users and devices trigger policy events?
- Which events require action, and which can remain informational?
A tool that creates constant alerts but rarely drives action increases workload and reduces trust. Clear reporting reduces exception churn and helps you defend policy changes to stakeholders.
4) Support secure browsing without breaking the business
Security that blocks legitimate work creates workarounds and shadow IT. A modern platform needs enough granularity to allow safe access while blocking the risky path.
5) Help uncover shadow IT and risky web behaviour
Web security overlaps with identity, SaaS adoption, and user risk. If your web security solution can surface trends, it helps you fix root causes rather than fighting individual incidents.
Veramed’s customer story shows how this looks in a real perimeter-free environment. Veramed grew as a cloud-only organisation without on‑premise perimeter security, then needed stronger web security controls as compliance expectations increased, including ISO 27001. TrustLayer combined web controls with cloud app security in one interface, which improved visibility into user behaviour and made monitoring practical for a lean IT function.
If you want to validate how proactive web security works in your environment, you can review Veramed’s customer story, Protecting staff in a perimeter-free world, then book a demo to see policy rollout speed and reporting detail.
Are web security solutions enough on their own?
Web security solutions reduce exposure at the point of access, but they work best when you pair them with identity controls and email security, backed by clear reporting processes.
What is real-time web threat protection?
Real-time web threat protection blocks or limits access to risky destinations as the user attempts to browse, instead of alerting after the session completes.
How does real-time web threat protection reduce workload?
Web threat protection earns value when it reduces the number of incidents that reach investigation stage.
The difference shows up in daily operations:
- Fewer credential resets after users land on fake sign-in pages
- Fewer endpoint checks after a browser download
- Fewer urgent support tickets triggered by blocked ransomware or malware sites
- More consistent policy enforcement across locations
Real-time protection cuts down the clean-up loop that consumes time. It also improves confidence in policy enforcement because the business sees consistent outcomes instead of sporadic alert spikes. This matters when IT teams need buy-in for tighter controls after an incident.
Where does TrustLayer fit?
TrustLayer positions Browse as a direct, endpoint-based layer that blocks threats before users click, with no DNS trickery or bolt-on infrastructure. TrustLayer designed it for organisations that need enforcement that follows the device and reporting that stays usable when users roam off-network. That matches what proactive web security requires: early enforcement and consistent coverage.
Explore TrustLayer Browse and TrustLayer One to see how endpoint enforcement and reporting work together when users roam.
If you want a comparison view, TrustLayer’s web filtering comparison guide benchmarks coverage and control quality for modern secure browsing.
For more examples of how UK organisations apply proactive web security in practice, explore the customer stories.
How can you move from reactive web security to proactive control?
Start with a control layer that blocks risky destinations at the point of access. Then use reporting to tighten policy and reduce exceptions, instead of adding more alerts.
TrustLayer Browse gives you endpoint-based enforcement that follows roaming devices and blocks threats before the click turns into an incident. It also keeps reporting usable, so IT departments focus on the few events that need action instead of chasing noise.
You can validate policy rollout speed and reporting detail in a demo.
If you want to compare approaches before you commit, use the web filtering comparison guide to benchmark coverage and control quality.
When you are ready to validate fit in your environment, book a demo or use the contact page to discuss rollout and policy requirements.