As businesses continue adopting cloud services, security challenges are evolving just as rapidly. Many threats in 2025 won’t come from obvious attacks but from overlooked weaknesses like misconfigurations, poor access controls, or unsanctioned apps. These hidden issues can expose sensitive data and disrupt operations without warning.
A modern approach to cloud defence includes using a Cloud Access Security Broker (CASB), alongside tools like Identity-as-a-Service (IDaaS) and Multi-Factor Authentication (MFA), to protect your organisation from the inside out. This blog will uncover critical cloud security gaps and explain how a CASB, like TrustLayer’s built-in solution, combined with IDaaS/MFA, helps close them.
What is a CASB?
A Cloud Access Security Broker (CASB) is a security layer between users and cloud services. It provides visibility, enforces policies, and prevents data loss across cloud platforms like Microsoft 365, Google Workspace, and Dropbox.
CASBs are essential in extending your organisation’s security policies to cloud environments. Whether you need to prevent data from being shared outside the company, detect risky user behaviour, or block malicious file uploads, a CASB gives you the centralised control required to manage it.
TrustLayer’s modular layer TL Browse, embeds CASB functionality directly into your environment, without the need for proxies or traffic rerouting. This helps IT teams secure distributed environments at scale while keeping operations simple and efficient.
Cloud security gaps you might be missing
Even with the best intentions, cloud environments often contain overlooked vulnerabilities. These gaps can create serious risks if not addressed proactively.
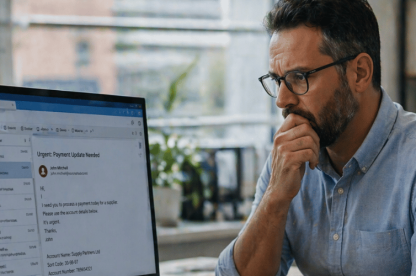
Shadow IT and lack of visibility
Employees often use cloud tools without IT approval, creating a shadow IT environment. While these tools help with productivity, they also bypass security oversight.
Why Shadow IT Matters
IT teams can’t monitor data movement or enforce security policies without visibility. CASBs help detect unauthorised apps and bring them under central control, reducing risk and maintaining compliance. With TrustLayer, these shadow apps can be quickly identified and managed, ensuring no one is working in the dark.
Why poor identity management matters
Over-permissioned or inactive accounts are common entry points for attackers. These accounts can lie dormant for months, waiting to be exploited. TrustLayer’s TL Users tracks identity posture in real time, automatically adjusting access based on user behaviour and device status. It also flags dormant accounts so you can revoke or reassign them promptly.
Misconfigured cloud settings
Cloud services offer advanced security features, but many organisations stick with default configurations or skip essential settings.
Why misconfigured settings matter
Misconfigurations, like publicly accessible file shares or missing MFA, are among the top causes of data breaches.
Insecure remote access
Remote workers may access business apps from unsecured devices or networks, expanding your attack surface.
Why insecure remote access matters
If one compromised endpoint connects to your cloud, the damage can ripple through your entire infrastructure. TrustLayer’s proxy-free setup enables secure access without slowing down user connections. It also enforces security policies based on user location, device health, and behavioural indicators, automatically adjusting risk levels for remote staff.
No real-time threat detection
Traditional tools often detect threats after they’ve caused damage, which is too late in a cloud-first environment.
Why real-time detection matters
Quick responses matter. A real-time CASB can detect suspicious activity immediately, enforce security policies, and even isolate users or apps before harm spreads. This proactive approach sets modern CASBs like TrustLayer apart from older, reactive security stacks.
Why legacy tools can’t keep up
Many businesses still depend on traditional security stacks built for on-premise systems. These tools often:
- Require on-site agents
- Need complex integrations
- Slow down access with traffic rerouting
This creates friction for users and extra work for IT teams. For MSPs managing multiple clients or large organisations handling thousands of users, it’s simply unsustainable.
TrustLayer offers a cloud-native alternative. Our CASB features are built directly into modular components, with no proxies, slowdowns, or headaches. Choose the tools you need and deploy them in hours, not weeks.
How TrustLayer bridges the cloud security gap
TrustLayer One is a modern cybersecurity platform built for scale, speed, and simplicity. Key modules include:
- TL Users – Monitor identity and access in real time.
- TL Browse – Protect SaaS and web activity without rerouting traffic
- TL Posture – Detect risky devices and apply automated controls
- TL Mail – Block phishing and threats at the inbox level
Each module can be used individually or combined into one streamlined solution. With modular pricing and self-serve deployment, TrustLayer gives you only what you need, nothing more, nothing less.
This flexibility means your IT team can quickly roll out defences where needed most, whether securing remote endpoints, enforcing access controls, or locking down shadow apps, without adding operational drag.
How to get started with CASB
If your team relies on cloud apps, the risks are real, but manageable. TrustLayer makes it easy to strengthen your security with built-in CASB protection that scales with your business.
Our platform is designed to meet the needs of real-world IT teams and MSPs who want clarity, control, and confidence, without the bloat or delays of traditional solutions.
Ready to secure your cloud environment for 2025?
Contact the TrustLayer team to learn how we can help you reduce risk and simplify operations through s i98marter cloud security.