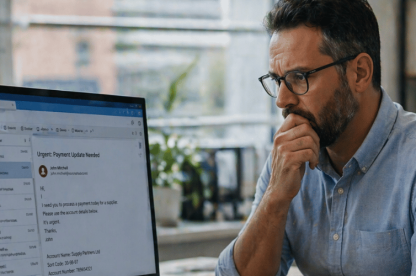
Recent reporting around Salesforce Experience Cloud showed how quickly a cloud data breach can start when a business does not control guest access and cloud settings tightly. Attackers reportedly exploited misconfigured guest user settings on public-facing sites and accessed customer data, while Salesforce said customer configuration caused the issue, not a flaw in the platform itself. That’s exactly why a CASB matters for UK SMEs relying heavily on SaaS. It helps businesses see cloud use more clearly and control risky access earlier.
Cloud data breaches do not always start with malware or a dramatic system failure. Many start when cloud use grows faster than the business can monitor, control, and govern it. A business rolls out a SaaS platform quickly. It leaves guest access wider than intended. A cloud app connects to another tool before anyone reviews the risk properly. People grant permissions and then leave them alone.
The question is simple: can a CASB help smaller businesses reduce cloud data breach risk when SaaS use grows faster than internal oversight? For businesses that need that visibility in practice, TrustLayer CASB is built to help IT leads and internal security owners see cloud use more clearly, control risky access earlier, and reduce the gaps that let exposure build unnoticed.
What is a CASB, in simple terms?
A CASB is a cloud access security broker. It helps a business see and control how people use cloud applications.
Most businesses now rely on a growing mix of SaaS tools, file-sharing platforms, collaboration apps, browsers, and cloud-connected services. Once that mix expands, the business can lose sight of which apps people use and where risky access starts. This layer gives the business a clearer view of that cloud activity, which helps smaller businesses spot risky use before it turns into a bigger problem.
How do cloud data breaches happen in SaaS-heavy environments?
Misconfigured access can expose more than people expect
A cloud data breach does not always start with an attacker breaking through a hardened perimeter. It can start when a business leaves access settings open for too long, exposes too much through guest permissions, or fails to revisit an app configuration after rollout.
The Salesforce story matters because it shows how cloud risk builds. This was not a straightforward platform breach. Access, permissions, and oversight had already started to drift apart.
Shadow IT creates cloud risk outside formal oversight
Many SMEs use more cloud tools than they realise. File-sharing apps, collaboration tools, browser-based AI tools, CRM add-ons, and project platforms often enter the business because staff can adopt them quickly and justify them easily.
That convenience creates risk when the business does not track which apps people use, what data those apps can reach, or how they connect to other tools. Once cloud use grows outside formal review, people move sensitive data into places the IT team never intended to oversee.
Tokens, integrations and trusted apps can widen exposure
Cloud risk also grows through app permissions, third-party integrations, and trusted access paths. An employee may connect one SaaS tool to another without thinking much about the permissions involved. Someone approves a browser prompt. Someone leaves an OAuth (open authorisation) connection in place. Access broadens quietly, often without anyone reviewing it again.
That is one reason cloud data breach prevention now needs more than basic login controls. The issue is not only who logs in. It is also which apps connect, what access they receive, and how long that access stays in place.
Can a CASB prevent cloud data breaches?
A CASB can help reduce some of the more common paths into cloud data exposure. It helps a business spot risky cloud use earlier and apply tighter control before risk drifts too far.
However, this control doesn’t solve every cloud security problem on its own. It doesn’t replace every other layer in the stack, and it doesn’t fix every misconfiguration by itself. It does reduce the blind spots that leave smaller businesses reacting too late.
Where it helps most
It helps most when the problem starts with visibility and control. It can show which cloud apps people use, identify unsanctioned services, and help the business apply policy before unmanaged cloud use turns into a bigger problem.
For SMEs, that means less time spent chasing unknown apps after the risk has already grown.
What it does not solve on its own
This control still sits inside a wider security picture. Email-led phishing still needs email protection. User mistakes still matter. Businesses may also need dedicated posture visibility and remediation to deal with misconfigurations.
The better question is simpler: will it reduce cloud exposure and give the business earlier control over risky cloud activity? In many cases, yes.
How does a CASB protect cloud applications?
A CASB protects cloud applications by helping businesses discover what people use, apply policies to cloud behaviour, and stop unmanaged or risky services slipping through without review.
For a small team, the value is practical and immediate. The team can see which cloud apps people use. It can decide which ones it approves and which permissions it allows. It can then act when activity falls outside policy.
This is where TrustLayer CASB becomes useful. It gives the team a clearer view of cloud app use and helps apply control before unmanaged services or risky permissions turn into a bigger issue.
Traditional security tools can miss what happens once data moves into cloud applications. A CASB helps close that gap by giving the business visibility and policy control inside cloud use itself, which makes it easier to catch risky activity earlier and cut down manual review.
Why do cloud security brokers matter more for UK SMEs?
Cloud security brokers matter more for UK SMEs because cloud use often grows faster than internal oversight. Smaller businesses often rely on the same cloud platforms, collaboration tools, and SaaS applications as much larger organisations. They usually do not have the same internal security resource overseeing that cloud use.
One IT lead or a small team often has to cover support, access issues, cloud administration, and security at the same time. That makes it harder to review every app, integration, and permission change by hand.
A CASB helps smaller teams see cloud usage more clearly, spot unsanctioned apps faster, and apply cloud control without the same level of manual review.
What should SMEs look for in this kind of cloud control?
For SMEs, the right platform should make cloud use visible first, then make practical control easier to apply.
Visibility first
The platform should show which cloud apps people use, who uses them, and where usage sits outside expected policy. If it cannot show sanctioned and unsanctioned app activity clearly, the business will struggle to reduce real cloud risk.
Policies that match real cloud use
The platform should not just generate alerts. It should help the business apply practical controls to cloud behaviour, permissions, and data handling. That gives the business something useful to act on, not just more noise to sort through.
A practical fit for a smaller team
For SMEs, it has to be usable. It should reduce manual review, simplify oversight, and fit into a wider layered model without becoming another management burden.
How should it fit into a layered security strategy?
This control gives businesses visibility and control over cloud application use. It works best inside a broader layered model.
Email protection still matters because many cloud compromise chains begin with a phishing email. User awareness still matters because staff decisions affect how apps, permissions, and data move. Misconfiguration visibility still matters because a risky setting in a cloud service can create exposure even when no one intended it.
This is where TrustLayer fits. TrustLayer CASB helps businesses see cloud application use more clearly and control it earlier. The CASB datasheet shows those capabilities in more detail. If the business needs broader layered coverage, TrustLayer One brings cloud, web, email, and user security together in one platform. If misconfiguration is part of the concern, TrustLayer Posture adds another useful layer.
See where your cloud app exposure starts
If cloud app use is growing faster than the team’s ability to review it, start with visibility. TrustLayer CASB helps businesses see sanctioned and unsanctioned cloud activity more clearly, apply control earlier, and close the gaps that let cloud exposure build unnoticed. That gives smaller teams a more practical starting point than trying to review every cloud service by hand.
The real risk is not cloud use. It is cloud use without control
Cloud use is now normal. SaaS growth is normal. Remote access and hybrid working are normal too. The real problem starts when businesses let cloud usage expand without enough visibility, policy control, or oversight to keep risk in check.
This control won’t solve every cloud security problem, but it can reduce some of the more common routes into cloud data exposure. It helps smaller businesses see risk earlier, apply more control, and respond sooner, which matters when one IT lead is trying to manage cloud use without much spare capacity.
If cloud visibility is the immediate gap, start with TrustLayer CASB. If the challenge is broader and touches cloud, web, email, and users at the same time, move up to TrustLayer One.